Market Research That Doesn't Take 6 Weeks.
Custom industry reports, investor lists, and competitive intelligence.For startup founders, B2B operators, and emerging VCs who need answers fast.
What We Do
We're your part-time research arm.
25-30 Page Reports
Real interviews, competitive analysis, and clear recommendations
Delivered in 5-7 Days
Not 6 weeks. Not "when we get to it."
AI-Enhanced Research
We combine scraping and synthesis to go deeper, faster
What We Build For You
VC Match Report
FOR: Pre-seed to Series A foundersWHAT: 25-50 handpicked VCs tailored to your startup, with contact info, investment thesis, and pitch strategyPRICE: $500-$1K
Market Research Report
FOR: B2B SaaS companiesWHAT: 20-30 page report with competitive landscape, customer interviews, and go/no-go recommendationPRICE: $1K-$2.5K
Industry Deep Dive
FOR: Emerging VCs & PE firmsWHAT: Sector-specific intelligence with key players, deal activity, whitespace opportunities, and operator interviewsPRICE: Custom pricing
This Is For You If...
You're a startup founder raising capital and wasting weeks cold-emailing VCs who don't actually invest in your space.You're a B2B operator deciding whether to build a new feature, enter a new market, or partner with someone, and you need real data, not gut feel.You're an investor hunting for edge in a new sector and can't afford the networks that bigger funds use.
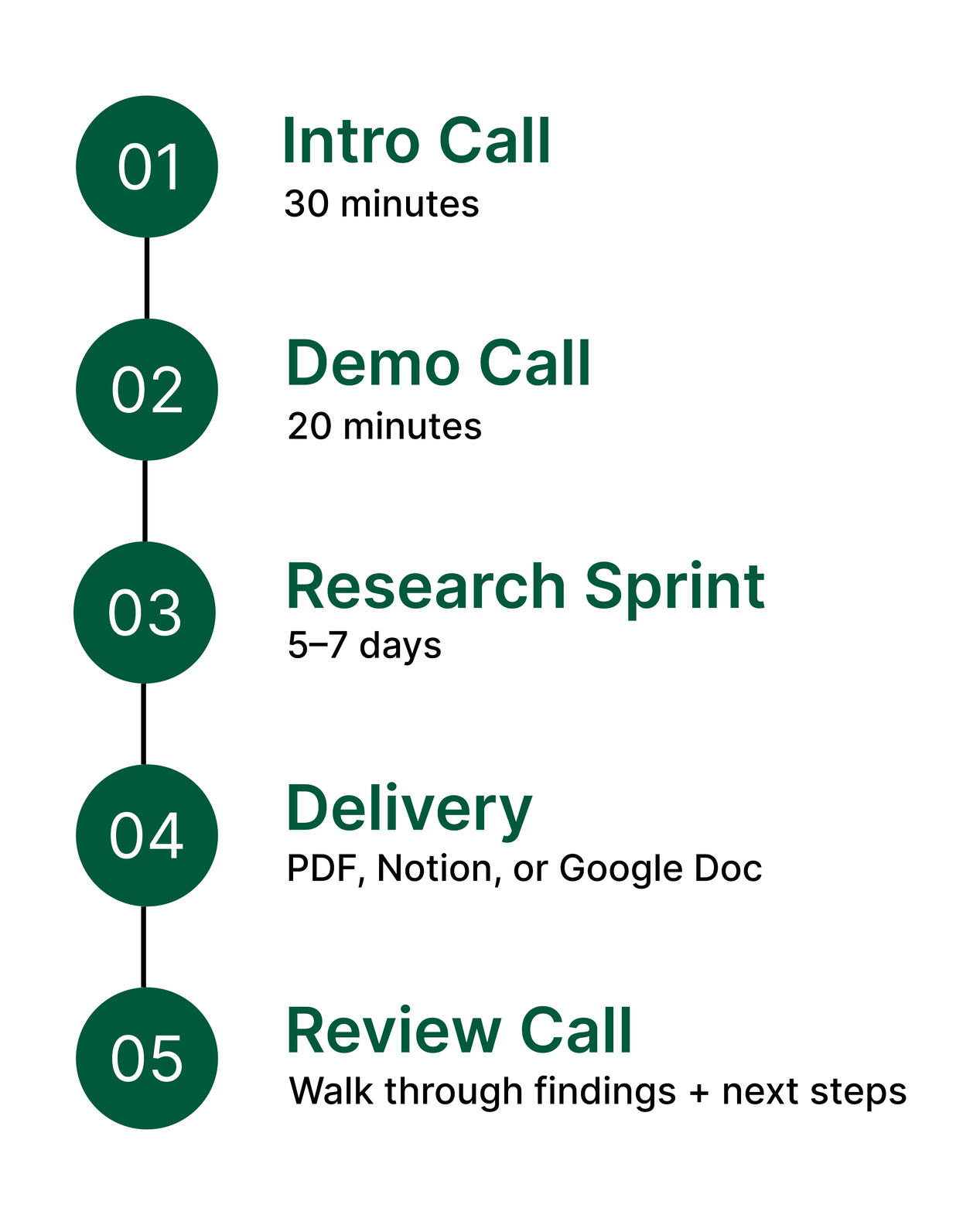
How It Works
STRATEGIC INTELLIGENCE